Is it possible for a singular security framework to effectively mitigate information security risks?
In the rapidly evolving digital landscape, information security has taken center stage as organizations across the globe face an unprecedented range of cyber threats.
From small businesses to multinational corporations, the push toward digital transformation has necessitated a reevaluation of security strategies to protect sensitive data and maintain operational integrity.
Against this backdrop, many organizations turn to security frameworks as the cornerstone of their information security programs. However, the question remains: Can a single security framework adequately address information security risks?
i. Understanding Security Frameworks
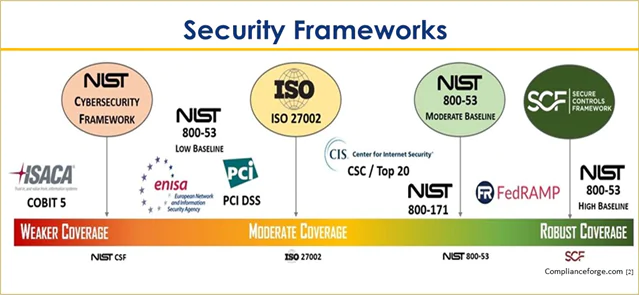
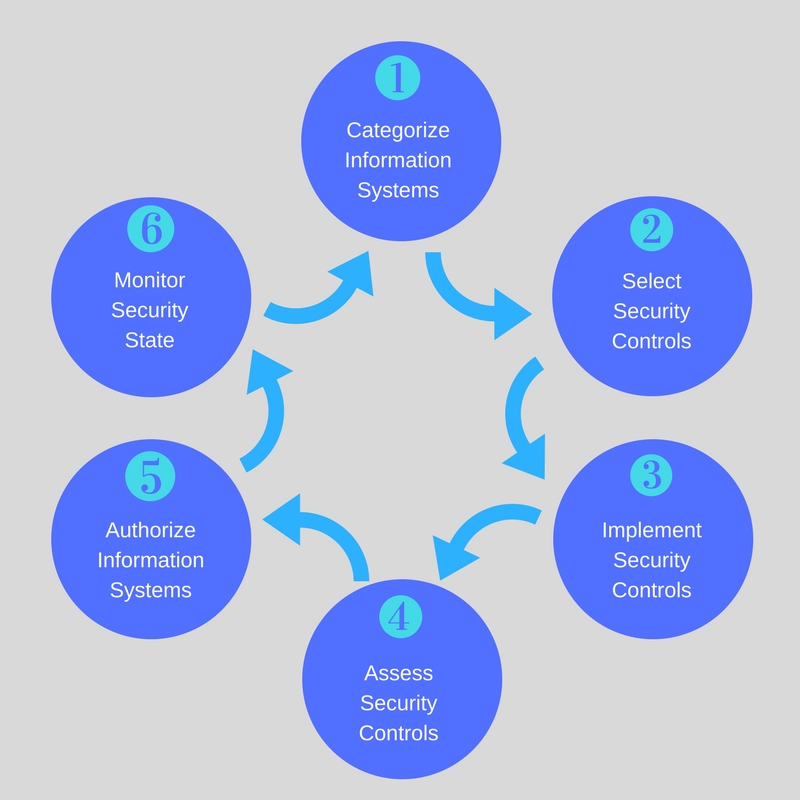
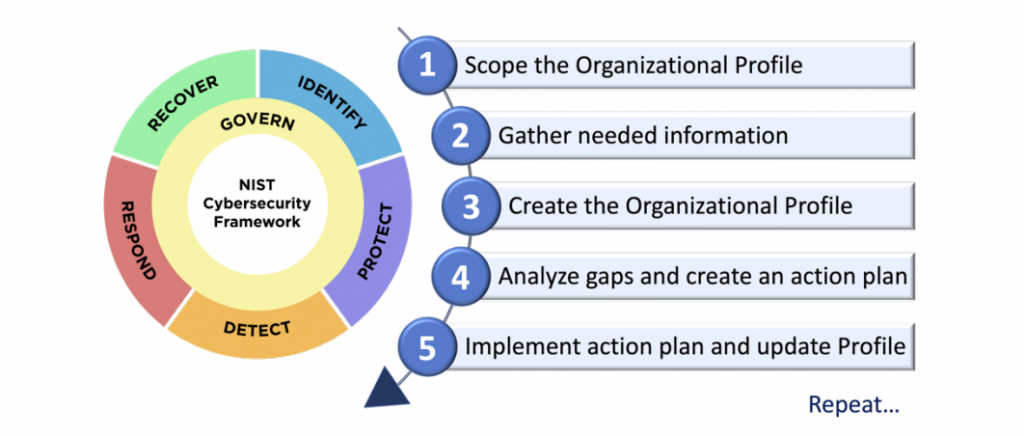
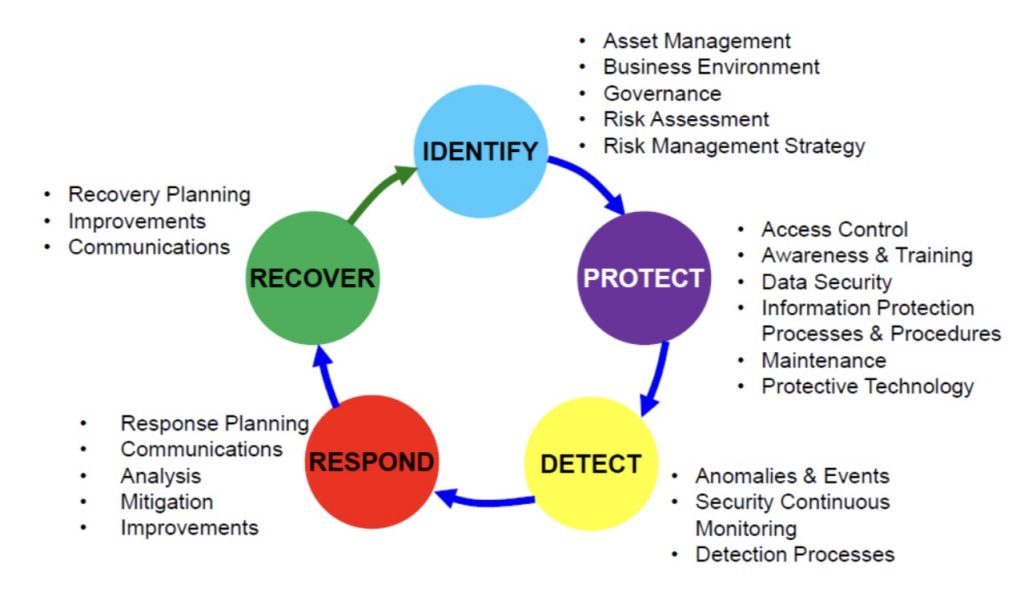
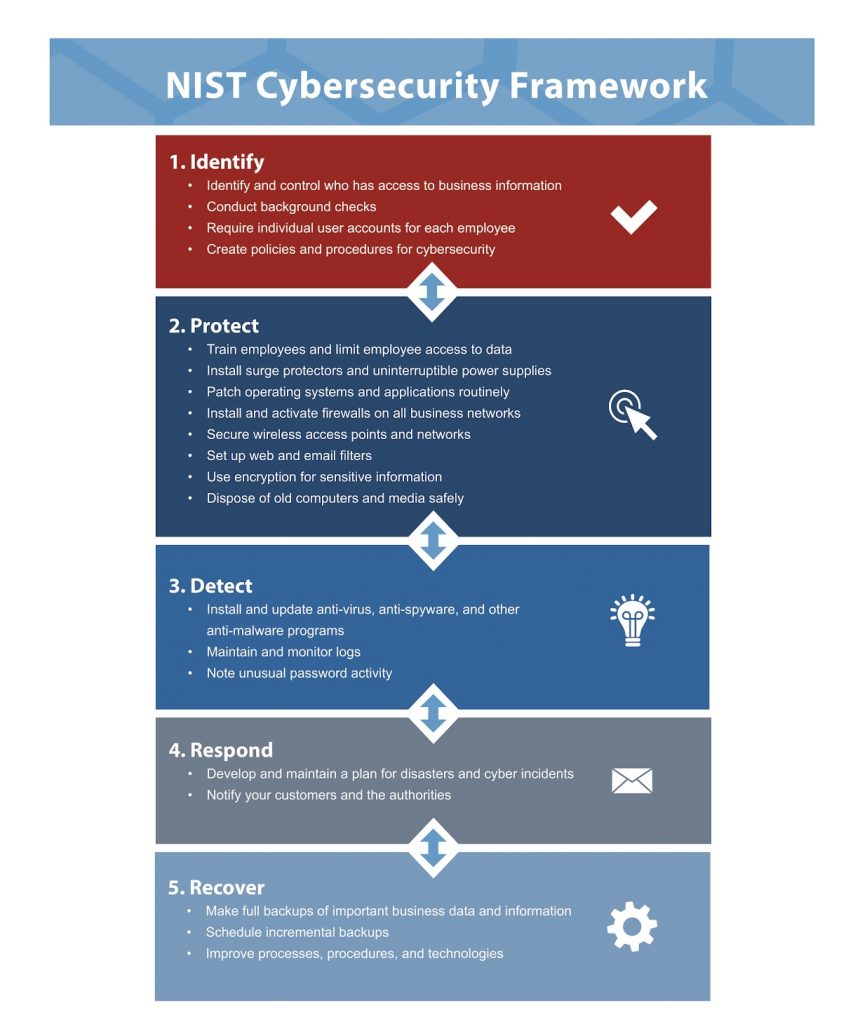
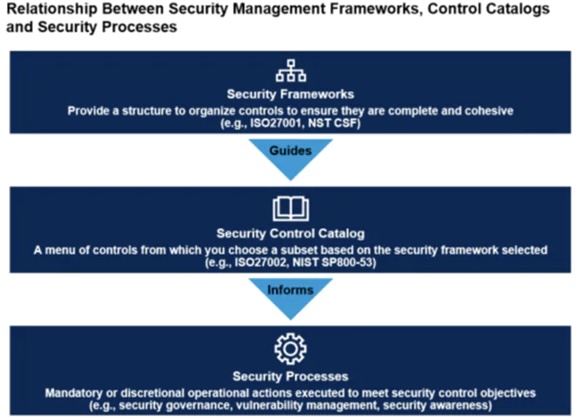
Security frameworks are structured sets of guidelines and best practices designed to mitigate information security risks. They provide a systematic approach to managing and securing information by outlining the policies, controls, and procedures necessary to protect organizational assets. Popular frameworks such as ISO 27001, NIST Cybersecurity Framework, and CIS Controls have been widely adopted across industries.
ii. The Benefits of Security Frameworks
Security frameworks offer several advantages:
o Standardized Approach: They provide a consistent methodology for implementing security controls.
o Risk Identification: They help organizations identify and prioritize security risks.
o Compliance: They can assist with meeting industry regulations and standards.
o Best Practices: They incorporate best practices for information security.
iii. The Argument for a Single Framework
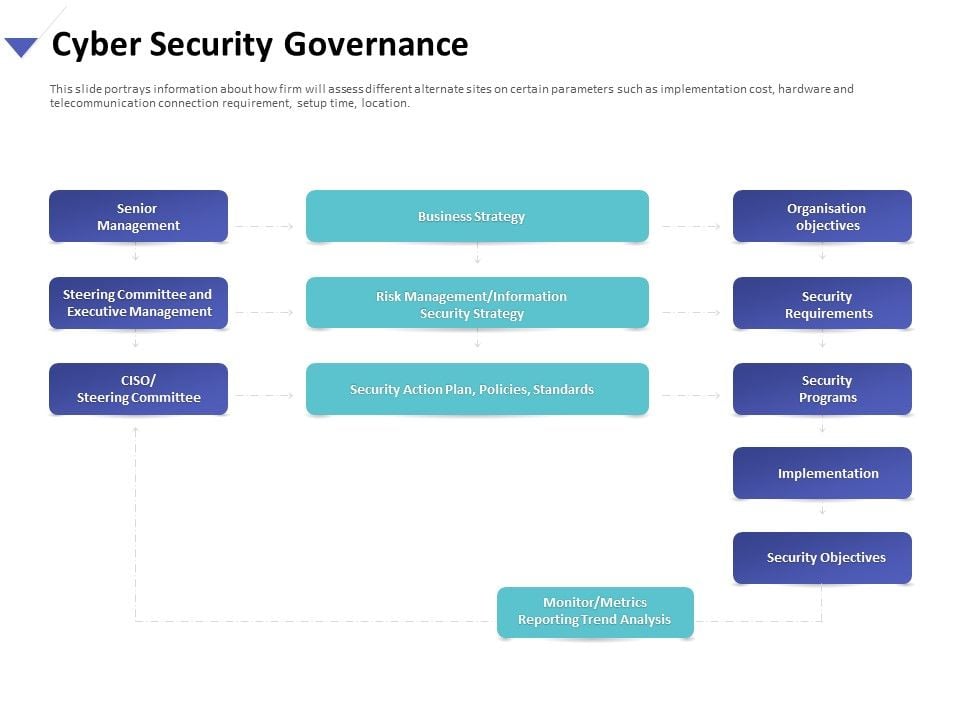
Adopting a single security framework can offer several benefits. For starters, it streamlines the process of developing and implementing a security strategy, providing a clear roadmap for organizations to follow. It also simplifies compliance efforts, as stakeholders have a singular set of guidelines to adhere to. Moreover, a single framework can foster a focused and cohesive security culture within an organization, with all efforts aligned towards the same objectives.
iv. The Challenges
However, relying solely on a single security framework may not be sufficient to address all aspects of information security for several reasons:
A. Diverse Threat Landscape

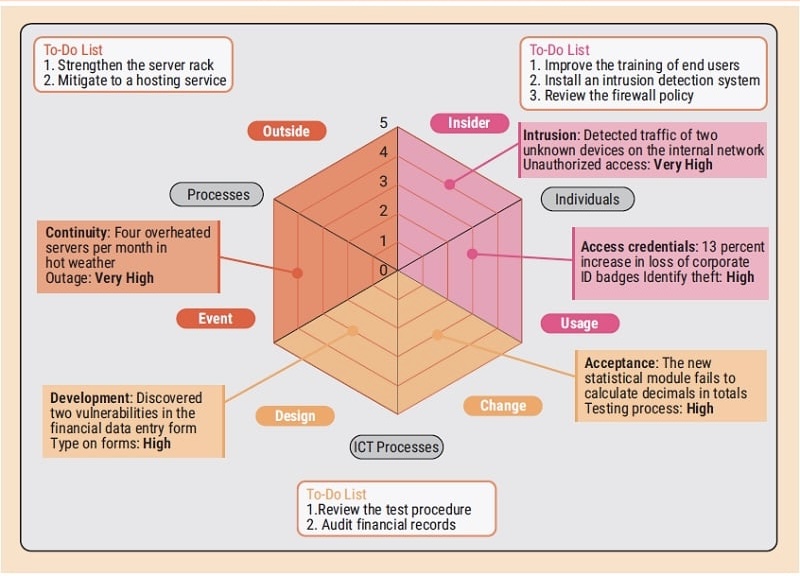
The cybersecurity landscape is constantly evolving, with new threats emerging regularly. A single framework may not cover all types of threats comprehensively, leaving organizations vulnerable to overlooked risks. For instance, while one framework may focus on network security, it might not adequately address social engineering attacks or insider threats.
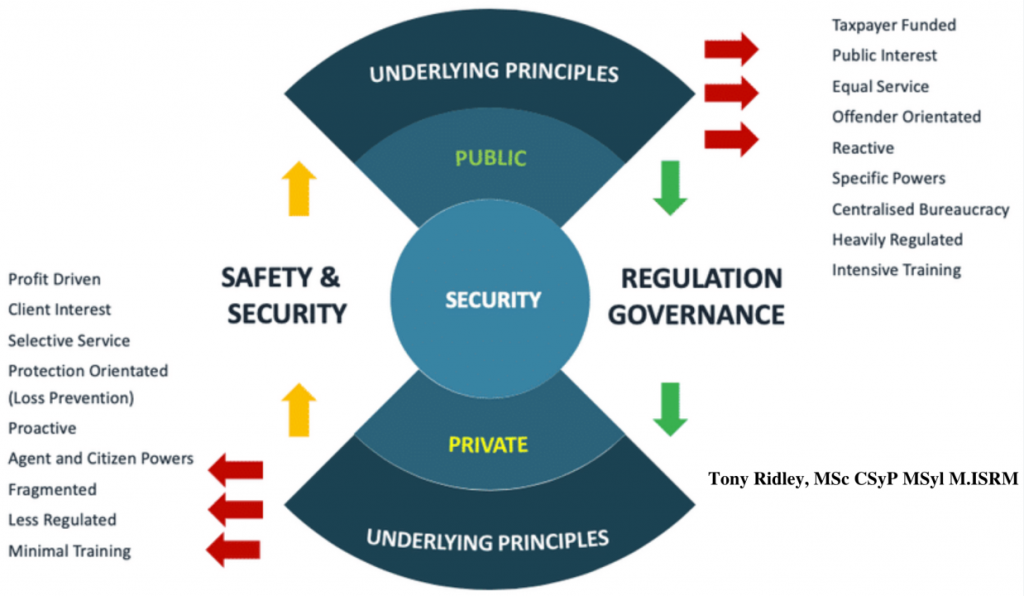
B. Industry-Specific Requirements
Different industries have unique security requirements and compliance mandates. A single framework may not align perfectly with industry-specific regulations and standards. Organizations operating in highly regulated sectors, such as healthcare or finance, may need to adhere to multiple frameworks and standards to ensure compliance and mitigate sector-specific risks effectively.
C. Organizational Specificity
Each organization has unique risks based on its industry, size, geographic location, and technological infrastructure. A one-size-fits-all approach may not cater to specific security needs.
D. Scalability and Flexibility
Organizations vary in size, complexity, and technological infrastructure. A one-size-fits-all approach may not accommodate the diverse needs of different organizations. A rigid adherence to a single framework may hinder scalability and flexibility, limiting the organization’s ability to adapt to changing threats and business environments.
E. Comprehensive Coverage
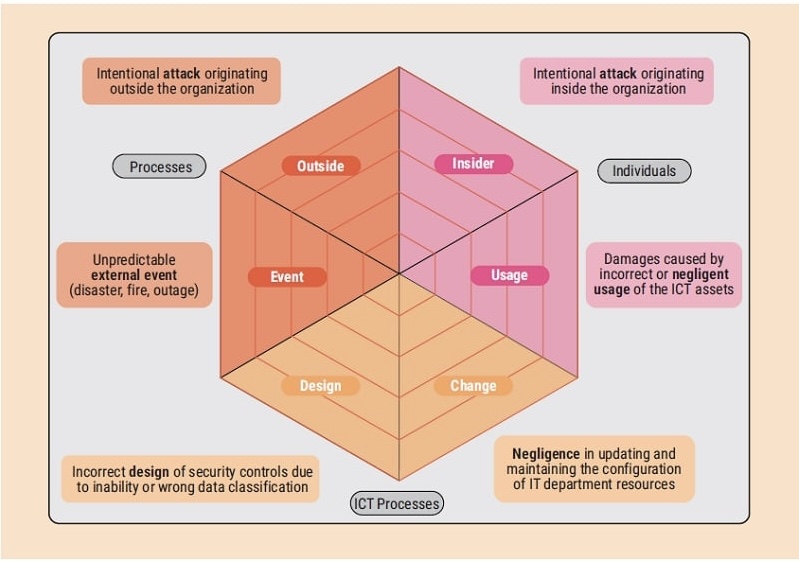
While some frameworks are comprehensive, they may lack depth in certain areas. For instance, a framework may cover a wide range of controls but not delve deeply into specific threats like insider threats or advanced persistent threats (APTs).
F. Emerging Technologies
Rapid advancements in technology, such as cloud computing, IoT, and AI, introduce new security challenges that traditional frameworks may not adequately address. Organizations leveraging cutting-edge technologies require agile security measures that can adapt to the unique risks associated with these innovations. A single framework may struggle to keep pace with the evolving technological landscape.
G. Integration Challenges
Many organizations already have existing security processes, tools, and investments in place. Integrating a new security framework seamlessly with the existing infrastructure can be complex and resource-intensive. A single framework may not easily integrate with other security solutions, leading to fragmented security measures and gaps in protection.
H. Regulatory Requirements
Organizations often operate under multiple regulatory environments. Relying on a single framework may not assure compliance with all the applicable laws and regulations, especially for organizations operating across borders.
v. Towards a Hybrid Approach
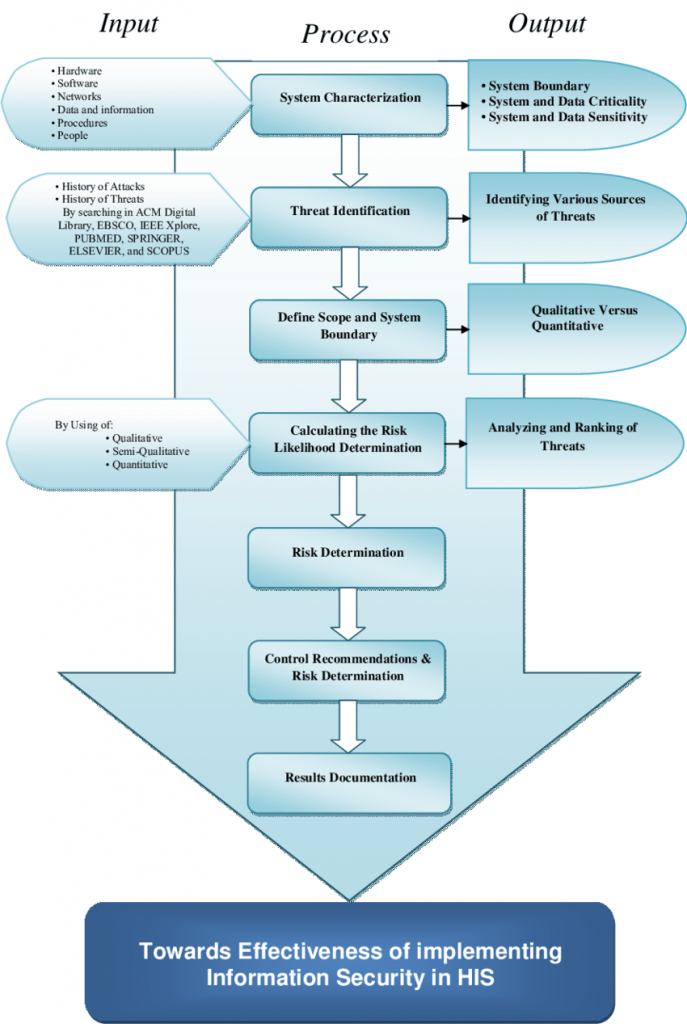
Given the limitations of a single-framework approach, organizations are increasingly adopting a hybrid or integrated approach to information security.
This involves leveraging the strengths of multiple frameworks to create a robust, flexible security posture that addresses the specific needs of the organization and adapts to the changing threat landscape.
A. Complementarity: By integrating complementary frameworks, organizations can cover a broader spectrum of security domains, from technical controls to governance and risk management.
B. Flexibility: A hybrid approach allows organizations to adapt their security practices as new threats emerge and as their own operational environments evolve.
C. Regulatory Compliance: Combining frameworks can help ensure that all regulatory requirements are met, reducing the risk of penalties and enhancing trust with stakeholders.
D. Best Practices: An integrated approach enables organizations to benefit from the best practices and insights distilled from various sources, leading to a more mature security posture.
vi. Complementing Frameworks with Best Practices and Custom Strategies
In addition to utilizing a primary security framework, organizations should integrate industry best practices, emerging security technologies, and custom strategies developed from their own experiences. This includes investing in ongoing employee training, staying updated with the latest cyber threat intelligence, and conducting regular security assessments to identify and mitigate vulnerabilities.
vii. Collaboration and Information Sharing
Collaboration and information sharing with industry peers, regulatory bodies, and security communities can also enhance an organization’s security posture. By sharing insights and learning from the experiences of others, organizations can stay ahead of emerging threats and adapt their security strategies accordingly.
viii. Conclusion

In conclusion, while adopting a single security framework can provide a solid foundation for managing information security risks, it should not be viewed as a panacea.
Organizations must recognize the limitations of a singular approach and supplement it with additional measures to address specific threats, industry requirements, and emerging technologies.
A holistic cybersecurity strategy should leverage multiple frameworks, tailored controls, continuous monitoring, and a proactive risk management mindset to effectively mitigate the ever-evolving cyber threats.
By embracing diversity in security approaches and staying vigilant, organizations can better safeguard their valuable assets and sensitive information in today’s dynamic threat landscape.
ix. Further references
TechTargethttps://www.techtarget.com › tipTop 12 IT security frameworks and standards explained
Secureframehttps://secureframe.com › blog › se…Essential Guide to Security Frameworks & 14 Examples
MDPIhttps://www.mdpi.com › …Risk-Management Framework and Information-Security Systems for Small …